What is BIMP?
The Base Image Management Platform
Introducing BIMP
Say hello to BIMP!
BIMP is a Base Image Management Platform. It’s a platform that you can use to manage your base images. Simple right? So why hasn’t anyone built this before?
If you’re building your applications as containers then you will no doubt be familiar with the Dockerfile. Imperfect as they are, they are the default format for building container images. The Dockerfile includes the configuration for the containers base image - the base layer on top of which you add your application and its dependencies.
The FROM: line in your Dockerfile is one of the most important interfaces of your software supply chain. The base image you select in that FROM: line is the gateway through which reams of Open Source Software enters your organisation. If any one of those packages is vulnerable your container is vulnerable.
Most companies have a policy here, they want developers to build their containers from a secure base image, a base image procured from a reputable supplier who provides SLAs and commitments on vulnerability patches.
All you need to do is select the right base image provider for you, and then make sure every FROM: line in every Dockerfile in every repo is kept up to date continuously. It’s not enough to select a secure base image today, you must keep that base image up to date constantly to ensure all new CVEs are fixed in a timely way.
BIMP automates this process end to end, putting base image CVE remediation on auto-pilot.
BIMP does this by ingesting your approved base image catalogue and then opening a pull request on every Dockerfile in every repo automatically.
The Gap
Most teams we’ve spoken to simply don’t update their base images, leaving them more and more vulnerable over time.
The problem is not technical. Updating a single line in a single file is not difficult. A single action could remediate tens, if not hundreds, of vulnerabilities. The problem is an organisational one.
The Development Team creates a Dockerfile, selects a base image and hooks it up to their build process. That is how it remains until someone (usually security) asks them to update it.
The Security Team is overwhelmed by risk signals, including vulnerability data from their chosen container scanner. They have to triage and prioritise those risks. They know what the fix is, but to make the fix they need to track down the right team and update the right file.
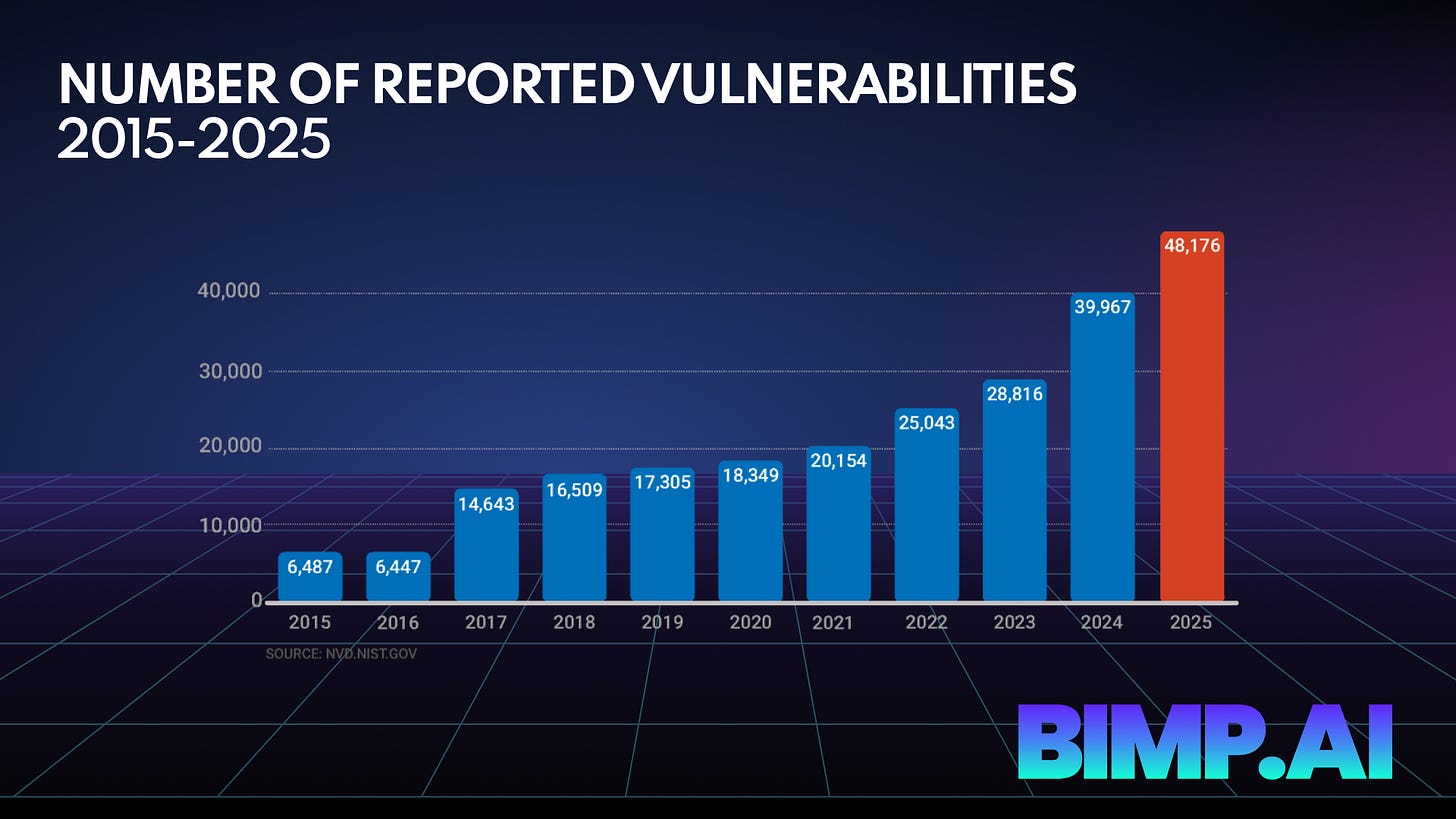
And this needs to happen continuously. There were over 48k new CVEs discovered in 2025 alone.
The Platform Team is curating a Golden Image catalogue of approved base images. They have worked with Security to select the right supplier and then they may have customised those purchased images ready to be used. They have told all of the Development Teams they support where to get the images, but they don’t know if every team has complied (and they suspect that many of the images have become insecure over time).
The solution is BIMP. A Base Image Management Platform. A Platform that makes Base Image Management completely automatic.
How Does BIMP Work?
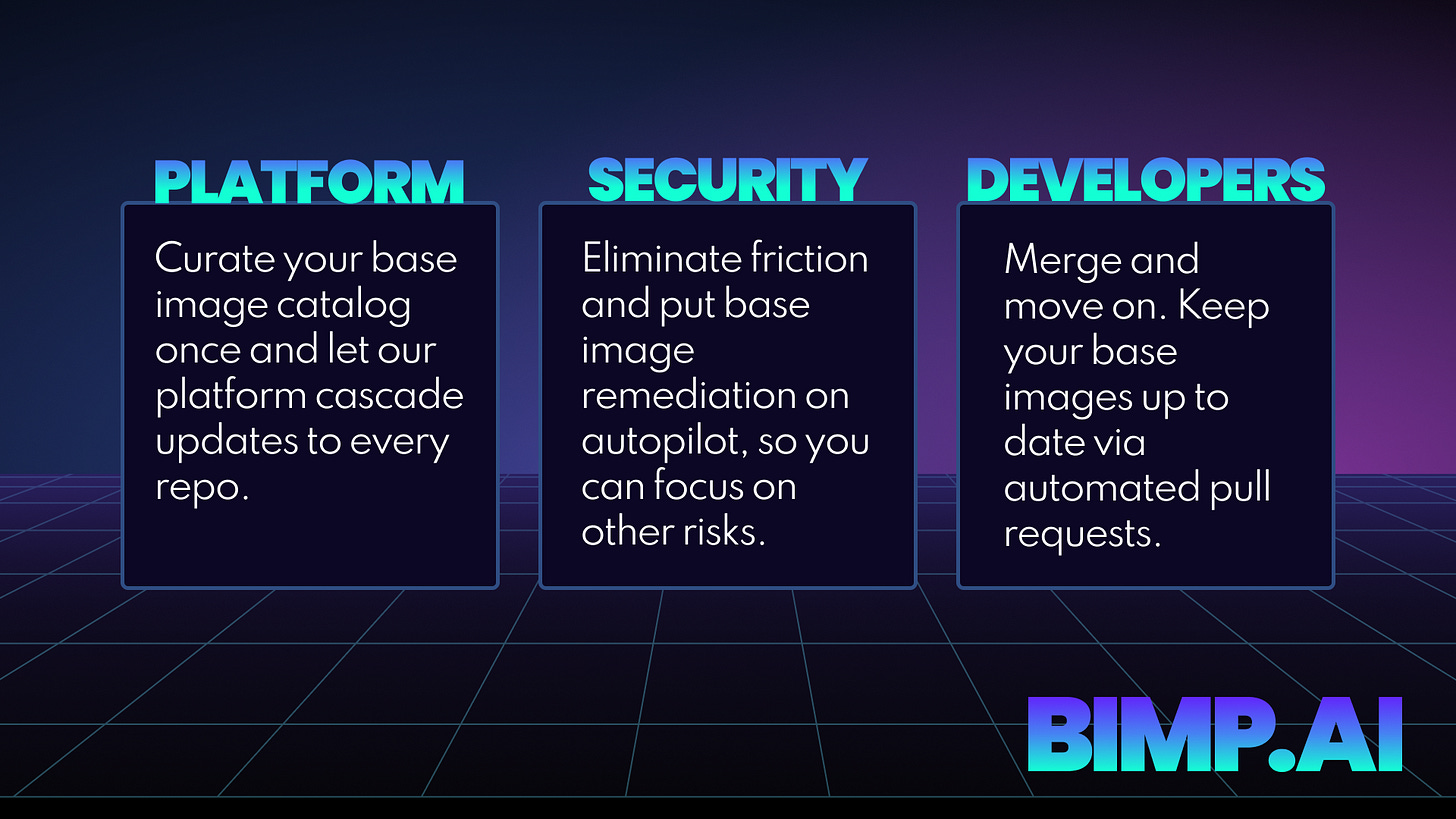
Platform
The Platform Team curates their approved base image catalog once. They set the policy in BIMP and let our platform cascade updates to every Dockerfile in every repo with a ready-to-merge pull request.
Developers
When it’s time to update their base image BIMP creates a PR on the Dockerfile. The Dev Team can simply merge and move on, never leaving their workflow.
Security
BIMP eliminates friction and puts base image remediation on autopilot. Security can be confident that all vulnerabilities discovered in the base image layer will be remediated automatically without them having to do any chasing at all. They are free to focus on other risks.
Isn’t this incredibly noisy?
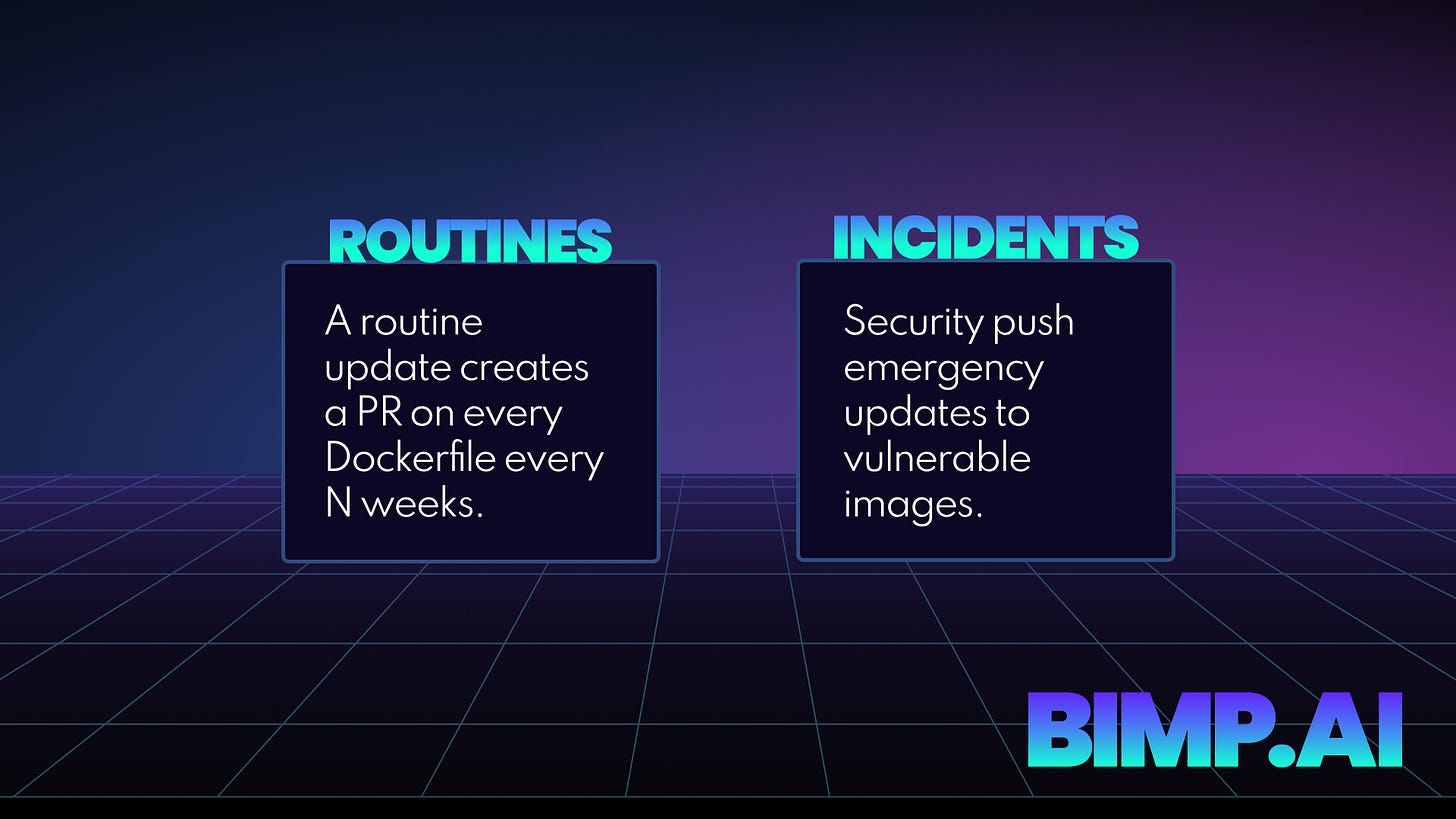
There are two types of updates in BIMP - Routines and Incidents.
Routine Updates
The most popular is the routine update - as an organisation you decide how often you want teams to process routine updates. That might be every 2 weeks or every 12 weeks, it’s up to you. The point is that there is always an update coming, no one gets left behind indefinitely and no-one needs to remember anything!
Security Incidents
However, sometimes you need to patch a vulnerability with more urgency than that. BIMP has an override feature that allows Security to push immediate updates to any repo that is impacted by a newly discovered vulnerability. These are tagged as BIMP-Security-Incidents.
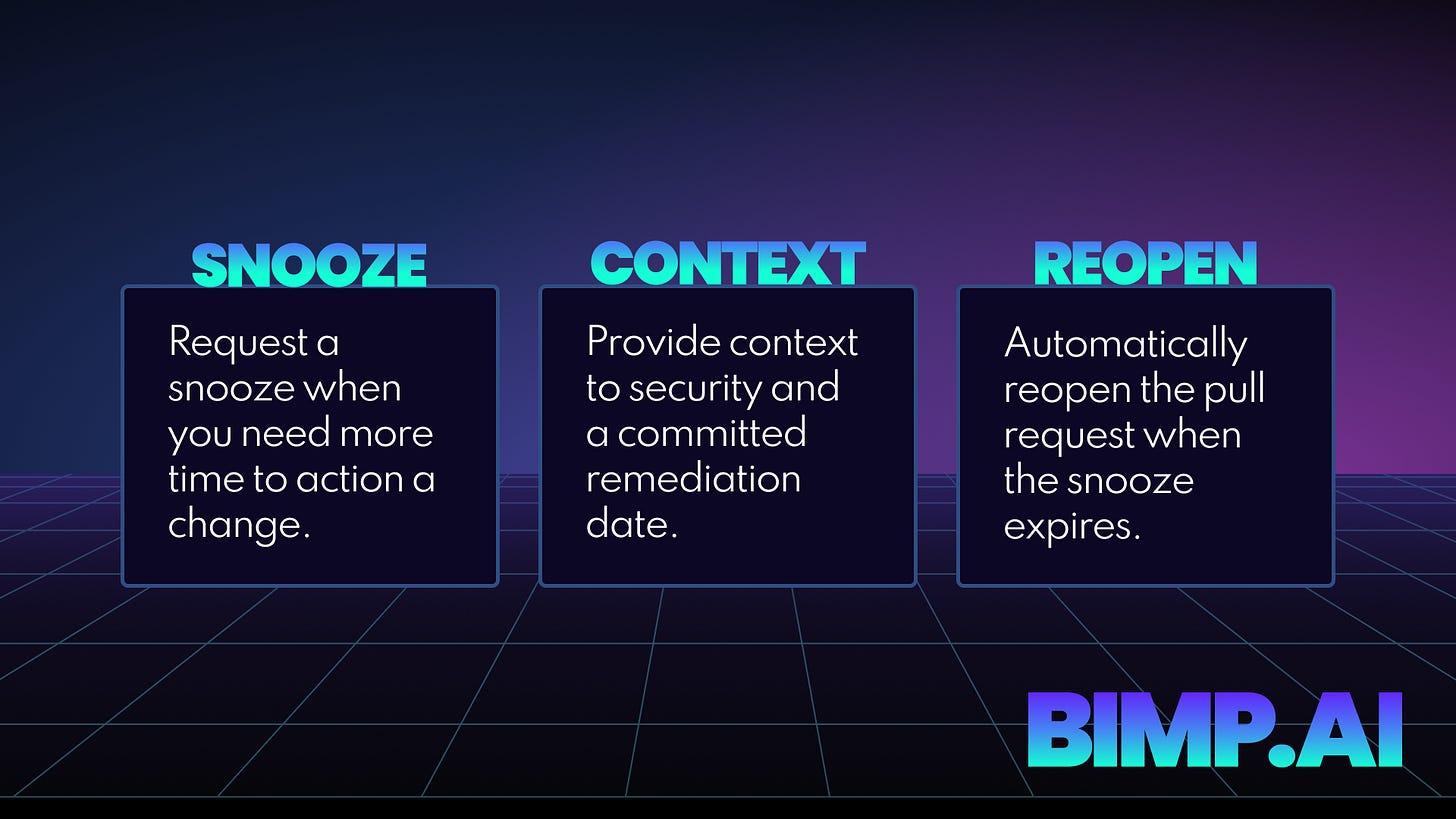
BIMP also gives the Development Team the opportunity to plan work on a schedule that works for them. If they can’t action a base image update immediately they can request a snooze. The snooze request is their commitment that they will do the work eventually, and security have the organisational context they need about the vulnerable base image.
BIMP reopens the pull request when the snooze expires so if ownership of the repo changes, the update isn’t forgotten.
Supply Chain Security in 2026
Agentic Hackers have arrived. Every day we see another newsworthy story of a supply chain attack or embarrassing compromise. Couple this with the tsunami of new vulnerabilities being discovered and the battle maintainers are fighting with code-slop contributions and we find most security teams in a pressure cooker.
Reviewing, triaging and prioritising risks worked when the volume of risks was small (well, smaller) and when most hackers needed years of experience to figure out novel ways to exploit vulnerabilities.
There’s a growing discomfort in security teams that ignoring the lower risks may not be a solid strategy in an age of Agentic Hackers. If there is a chink in your cyber-armor an agent will find it, and they won’t get tired of trying. Luckily, the same technology that helped create this pressure cooker can help us solve this problem.
Automation is the answer and AI unlocks huge opportunities for automation in our software development processes. Prioritisation is still important but we believe that you should fix the foundations by default. No triage, no prioritisation, no chasing - just fucking fix it.
Our Vision
We believe that action oriented security is the future. We aren’t another bad news dashboard full of risks. We start with the question “what needs to happen?” and then we automate that action end to end, so neither security or developers need to think about it.
Our vision is to secure the foundation of the software supply chain for everyone, by changing how the work gets done. Zero-CVE base images need to become the default and BIMP is going to get us there faster. Migrate in minutes not months.
Secure your container base images today. Be zero-day ready tomorrow.
Watch the demo on youtube or join the waitlist.